Understanding Website Security for Business People

"Our website isn't working and there's a scary Turkish message with a link to Paypal on the homepage!" typed Samantha in an email to the person who created her website. She was nervous. She thought, "are customers seeing this? What if a customer gives these scammers money? Am I responsible for this?"
A few minutes later she receives a reply, "We see it too. It looks like it's been hacked. I'll take a look and get right back to you." A sigh of relief comes over her but a wave of anxiety returns just moments later when the phone rings. A voice on the other end sounds cautious, "Good morning Samantha, this is the owner of Acme Web Company. It looks like your website was hacked and unfortunately, we can't restore it to the way it used to be. The last backup we have is from a year ago."
Samantha was devastated. They'd worked for years to build their online business and now they'd lost a year's worth of work overnight. She wondered, "How did this happen? How am I going to explain this to the company?"
Owning your Security
Does Samantha's plight sound familiar to you? You're not alone. Thousands of website owners find themselves in this exact situation every year but there's good news! With a little awareness and ownership, you can be much more prepared to prevent security disasters and to recover when they do (you can bet that they will).
First, we need to agree that your digital service provider (your web designer, developer or digital marketing guru) does not own your website. You own your website. They are contracted to provide services to you so that you can operate your online business more confidently. The same relationship is true of services like wealth management (it's your money), construction (it's your building), and medicine (it's your body). If you haven't signed a contract with someone specifically designating them as the service provider for security-related issues, the probability that somebody is watching your back is low.
Mapping the Wilderness
There are four basic areas in which security should be addressed for your site. Attackers can exploit each of these areas to take control of, or to use, your website to harm your business and your customers.
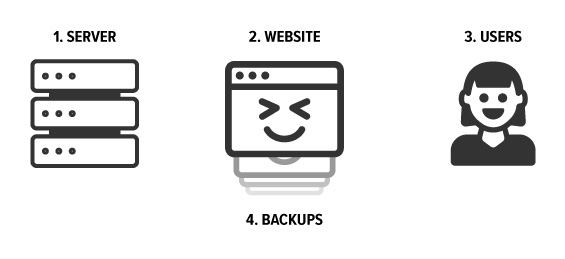
- Your web server is what sends you a page when you click a link on your site.
- Your website is the code and media which control what your website does and what data it has.
- Users are the people who use your website. Most of the time users are customers, but sometimes users are the people who log in and manage the content on your site.
- Backups are historical snapshots of what your website is at a given point in time. You can use these in case something goes wrong with your current website.
Secure the Server
Limit Access
Do you know who has access to your server? If your web hosting provider manages this for you, you should ask how they manage access for your hosting environment. As a general rule of thumb, the fewer people with access the better! At Omni, employees with access to hosting each have their own account and credentials, which helps us audit activity and manage access when employees join or leave the company. We can also grant access to specific accounts for you and your partners for the ultimate collaboration!
Web Application Firewall
A Web Application Firewall (or WAF) is like a bodyguard with special knowledge about how hackers might attack your website. We employee special WAF rules for Wordpress and Drupal sites that help stop a variety of attacks unique to those platforms. A WAF can even act as an extra level of protection preventing attackers from exploiting a Wordpress site that hasn't been updated in a while.
HTTPS
Browser makers (Google, Mozilla, Microsoft) have made a big effort over the past couple of years to ensure that users know when a website isn't secure. When a site isn't secure, attackers could steal your credentials (login, payment information, even SSNs) through a variety of ingenious attacks. You likely wouldn't even know it happened! The industry is pretty clear on this; sites that aren't using HTTPS will be less recommended in searches and browsers will make an effort to prevent users from accessing them.
Secure the Website
CMS Updates
If you have a Content Management System like WordPress or Drupal, there are regular security updates available to you. These security updates are available for free and you should have a plan for regularly applying and testing these. It's important to understand that when a CMS releases a security update to fix an exploit, hackers are also informed of the exploit and begin trying to take advantage of sites that aren't updated. We offer an affordable "maintenance agreement" to our customers which covers proactive updates to sites and routine tune-up activities.
Build your Site for Security
If you're planning to build a new website or application, make sure you have a conversation with your partners about your concerns related to security. While the makers of WordPress and Drupal do maintain the underlying security of the application, they don't monitor security issues unique to features that you've built for your project.
Be especially wary of partners who assure you that there is no risk related to new feature development. I've stumbled upon more than a few sites storing insecure social security number data and medical records — much to the horror of site owners! The best developers know that there is some degree of risk to be assessed and managed when building new features.
Enhance your Site with Security Features
There are some security issues which are pervasive enough that software communities have built features which solve them and are available for your site. These security features are unique to each platform, but in Drupal we use a few on just about every site;
- Captcha and Honeypot to ensure that only humans are completing your forms (because nobody likes spam from Russian bots).
- Security Kit for extra protection against a variety of common exploits.
- Paranoia to scan and evaluate your site for potential exploits.
Use only Security Team Approved Modules (if there is a security team)
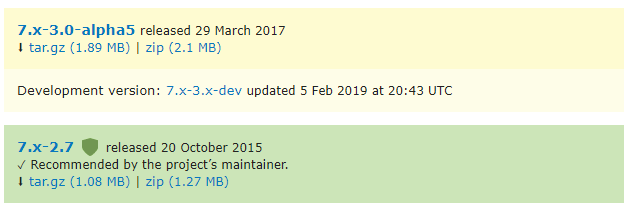
The Drupal CMS' Security Team evaluates and approves projects, blessing them with the green release color when they've passed review. Ask your provider how they can evaluate the security of third-party code they've added to your project. Often teams are adding third-party features to your site without ever considering the security implications.
Backups
Even organizations who spend millions of dollars annually on security may eventually find themselves in the midst of a catastrophe. When the worst outcomes come to pass, it's important that you have backups available to restore service and availability.
You should have conversations with your provider around some common backup tactics;
- Where are your backups stored? Who has access to them?
- How often do backups occur?
- Are our backups frequent enough?
- How easy is it to restore a backup?
- What happens after a backup is restored? How do we prevent catastrophe from occurring again?
User Security
Even after all the effort directed towards securing technology is complete, we still need to consider what some analysts consider to be the weakest link in your cybersecurity plan; people.
Enforce Strong Password Policies
Depending on the kind of site you operate, you may have many different types of users: customers, managers, writers, marketers, administrators. They all need to log into the site with credentials, and all too often users set passwords as simple as "123456" when left to their own devices. Your chosen system should allow developers to configure a number of password strength metrics that prevent users from creating insecure passwords.
Limit User Capabilities by Role
What if your website's customers suddenly found themselves with the ability to change your homepage? Samantha's plight might sound horrific, but I can't imagine that this situation would create calm conversations around the office either.
Systems like Drupal allow developers to create "roles" for users that grant them unique privledges and access to areas of the site. For example, it's common to prevent non-technical site editors from embedding code from third-party websites. If not in place, hackers could trick an editor into pasting malicious code to your site, which in turn might trick your visitors into giving hackers sensitive information.
Knowledge is the Key to Secure Ownership
I hope this article has given you a greater sense of ownership over your digital assets, a better understanding of the security landscape, and a path towards better understanding your current security situation.
If this feels overwhelming to you, you're not alone! Companies have trusted Omni for decades to guide them through these issues and ensure that their property is secure. Come see us to discuss what keeps you up at night. We'd love to talk to you!

Aaron Silber
Our resident digital polymath, Aaron shares a wide knowledge of how products and services are designed and built for the web.